End-to-End Intelligence Gathering Part 3: Intelligence in Action – Dissemination & Impact
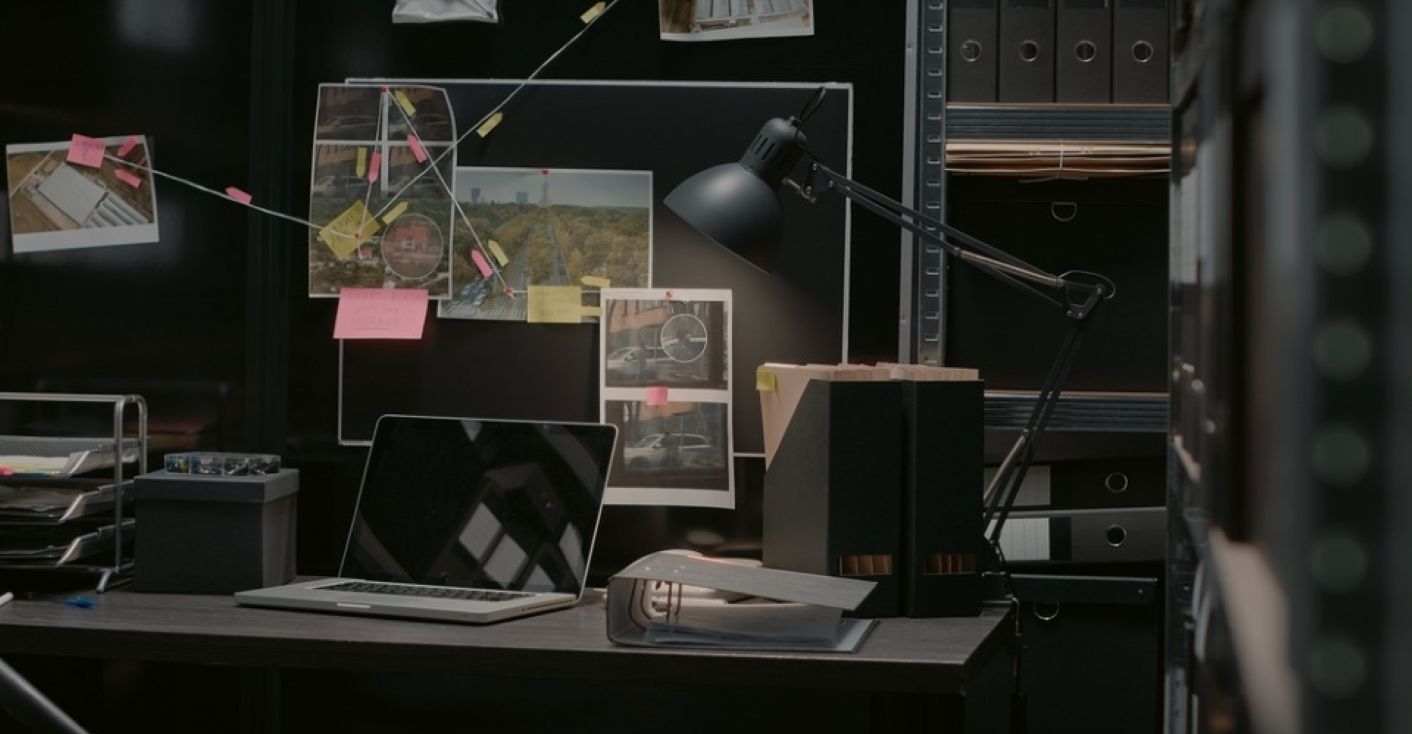
Lawful intelligence gives investigators access to vast, complex data sets. Automated tools allow analysis at massive scale, but cases are built by humans, making the usability of such solutions critical.